FBI Dismantles QakBot Malware, Frees 700,000 Computers, Seizes $8.6 Million
A coordinated law enforcement effort codenamed Operation Duck Hunt has felled QakBot, a notorious Windows malware family that’s estimated to have compromised over 700,000 computers globally and facilitated financial fraud as well as ransomware.
To that end, the U.S. Justice Department (DoJ) said the malware is “being deleted from victim computers, preventing it from doing any more harm,” adding it seized more than $8.6 million in cryptocurrency in illicit profits.
The cross-border exercise involved the participation of France, Germany, Latvia, Romania, the Netherlands, the U.K., and the U.S., alongside technical assistance from cybersecurity company Zscaler.
The dismantling has been hailed as “the largest U.S.-led financial and technical disruption of a botnet infrastructure leveraged by cybercriminals.” No arrests were announced.
QakBot, also known as QBot and Pinkslipbot, started its life as a banking trojan in 2007 before morphing into a general-purpose Swiss Army knife that acts as a distribution center for malicious code on infected machines, including ransomware, unbeknownst to the victims.

Some of the major ransomware families propagated through QakBot comprise Conti, ProLock, Egregor, REvil, MegaCortex, and Black Basta. QakBot administrators are said to have received fees corresponding to approximately $58 million in ransoms paid by victims between October 2021 and April 2023.
“QakBot was a key enabler within the cyber crime ecosystem, facilitating ransomware attacks and other serious threats,” Will Lyne, head of cyber intelligence at the U.K.’s National Crime Agency (NCA), said in a statement.
The counteroffensive against QakBot follows a similar takedown of Emotet in October 2020, which has since resurfaced following a major disruption to its backend infrastructure.
Typically distributed via phishing emails, the modular malware also comes fitted with command execution and information harvesting capabilities. It has seen constant updates during its lifetime, with the actors (codenamed Gold Lagoon or Mallard Spider) known to take extended breaks each summer before resuming their spamming campaigns.
“The victim computers infected with QakBot malware are part of a botnet (a network of compromised computers), meaning the perpetrators can remotely control all the infected computers in a coordinated manner,” the DoJ said.
The joint effort, according to court documents, enabled access to QakBot infrastructure, thereby making it possible to redirect the botnet traffic to and through servers controlled by the U.S. Federal Bureau of Investigation (FBI) with the ultimate goal of neutralizing the “far-reaching criminal supply chain.”
Specifically, the servers instructed the compromised endpoints to download an uninstaller file that’s designed to untether the machines from the QakBot botnet, effectively preventing additional payloads from being delivered.
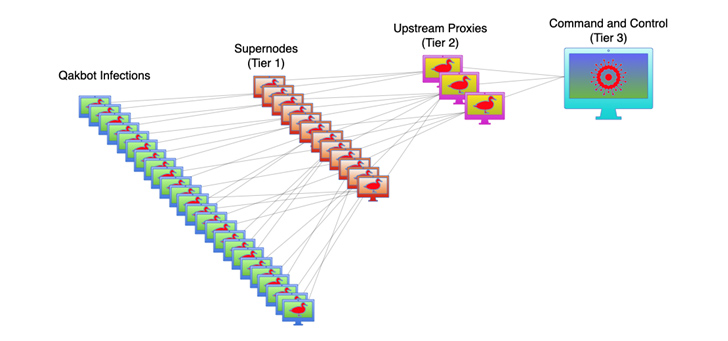 |
| Image Source: CISA |
Secureworks Counter Threat Unit (CTU) said it detected the botnet distributing shellcode to infected devices on August 25, 2023, which “unpacks a custom DLL (dynamic-link library) executable that contains code that can cleanly terminate the running QakBot process on the host” by means of a QPCMD_BOT_SHUTDOWN command.
“The victims [in the U.S.] ranged from financial institutions on the East Coast to a critical infrastructure government contractor in the Midwest to a medical device manufacturer on the West Coast,” FBI Director Christopher Wray said.
Detect, Respond, Protect: ITDR and SSPM for Complete SaaS Security
Discover how Identity Threat Detection & Response (ITDR) identifies and mitigates threats with the help of SSPM. Learn how to secure your corporate SaaS applications and protect your data, even after a breach.
QakBot has demonstrated a higher level of complexity over time, rapidly shifting its tactics in response to new security guardrails. For instance, after Microsoft disabled macros by default in all Office applications, it began abusing OneNote files as an infection vector earlier this year.
The sophistication and adaptability is also evident in the operators’ ability to weaponize a wide range of file formats (e.g., PDF, HTML, and ZIP) in its attack chains. A majority of QakBot’s command-and-control (C2) servers are concentrated in the U.S., the U.K., India, Canada, and France (FR). Its backend infrastructure is located in Russia.
QakBot, like Emotet and IcedID, employs a three-tiered system of servers to control and communicate with the malware installed on infected computers. The primary purpose of the Tier 1 and Tier 2 servers is to forward communications containing encrypted data between QakBot-infected computers and the Tier 3 server which controls the botnet.
As of mid-June 2023, 853 Tier 1 servers (aka supernodes) have been identified in 63 countries, with Tier 2 servers functioning as proxies to conceal the main C2 server. Data gathered by Abuse.ch shows that all QakBot servers are currently offline.
“QakBot is a highly sophisticated banking trojan malware, strategically targeting businesses across different countries,” Zscaler researchers noted in an exhaustive analysis published in late July 2023.
“This elusive threat employs multiple file formats and obfuscation methods within its attack chain, enabling it to evade detection from conventional antivirus engines. Through its experimentation with diverse attack chains, it becomes evident that the threat actor behind QakBot is continuously refining its strategies.”
QakBot has also been one of the most active malware families in the second quarter of 2023, per HP Wolf Security, leveraging as many as 18 unique attack chains and clocking 56 campaigns over the time period, underscoring the e-crime group’s penchant for “quickly permuting their tradecraft to exploit gaps in network defenses.”