Two High-Risk Security Flaws Discovered in Curl Library – New Patches Released
 |
| Image Source: JFrog Security Research |
Patches have been released for two security flaws impacting the Curl data transfer library, the most severe of which could potentially result in code execution.
The list of vulnerabilities is as follows –
- CVE-2023-38545 (CVSS score: 7.5) – SOCKS5 heap-based buffer overflow vulnerability
- CVE-2023-38546 (CVSS score: 5.0) – Cookie injection with none file
CVE-2023-38545 is the more severe of the two, and has been described by the project’s lead developer, Daniel Stenberg, as “probably the worst Curl security flaw in a long time.” It affects libcurl versions 7.69.0 to and including 8.3.0.
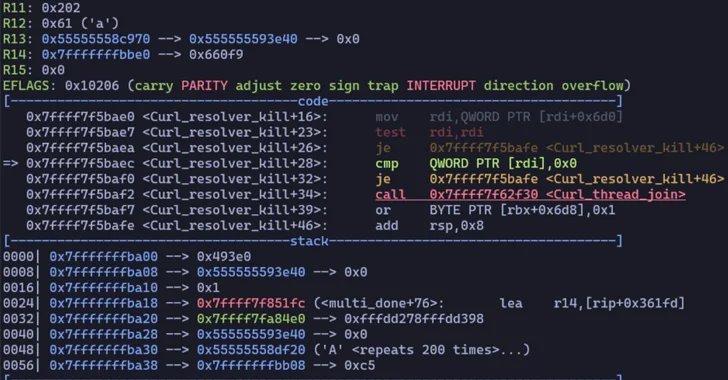
“This flaw makes Curl overflow a heap-based buffer in the SOCKS5 proxy handshake,” the maintainers said in an advisory. “When Curl is asked to pass along the hostname to the SOCKS5 proxy to allow that to resolve the address instead of it getting done by Curl itself, the maximum length that hostname can be is 255 bytes.”
“If the hostname is detected to be longer than 255 bytes, Curl switches to local name resolving and instead passes on the resolved address only to the proxy. Due to a bug, the local variable that means ‘let the host resolve the name’ could get the wrong value during a slow SOCKS5 handshake, and contrary to the intention, copy the too long hostname to the target buffer instead of copying just the resolved address there.”
Curl said the vulnerability could likely be exploited without the need for a denial-of-service attack and an overflow could be triggered with a malicious HTTPS server performing a redirect to a specially crafted URL.
“Seeing that Curl is an ubiquitous project it can be assumed with good confidence that this vulnerability will get exploited in the wild for remote code execution, with more sophisticated exploits being developed,” JFrog said. “However – the set of pre-conditions needed in order for a machine to be vulnerable is more restrictive than initially believed.”
“A valid exploit would require an attacker to trigger code execution by, for example, passing a hostname to a web app that would trigger the code execution in Curl,” Johannes B. Ullrich, the dean of research at the SANS Technology Institute, said. “Next, the exploit only exists if Curl is used to connect to a SOCKS5 proxy. This is another dependency, making exploitation less likely.”
The second vulnerability, which impacts libcurl versions 7.9.1 to 8.3.0, allows a bad actor to insert cookies at will into a running program using libcurl under specific circumstances.
Patches for both flaws are available in version 8.4.0 released on October 11, 2023. Specifically, the update ensures that Curl no longer switches to local resolve mode if a hostname is too long, thereby mitigating the risk of heap-based buffer overflows.
“This family of flaws would have been impossible if Curl had been written in a memory-safe language instead of C, but porting Curl to another language is not on the agenda,” Stenberg added.